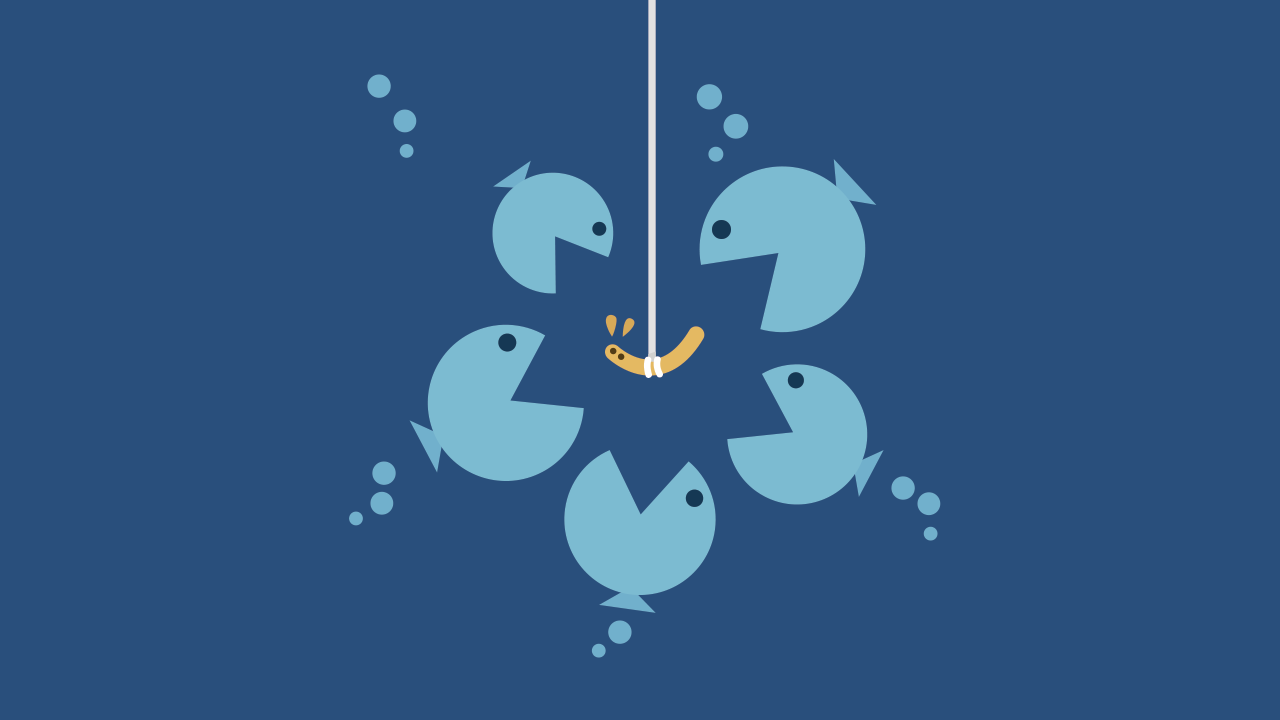
Phishing scams involve sending deceptive email messages that appear to be from trustworthy sources, such as a person you know or a legitimate organization you do business with. Phishing also occurs via text messages (SMS), which is referred to as SMS phishing or “smishing.” Scammers use this ploy to gain your trust so you will click on a link to a fraudulent website, share private information, or open an attachment on your phone, tablet or computer.
What Happens If You Click on a Phishing Link?
Clicking on a phishing link or opening an attachment in one of these messages may install malware, like viruses, spyware or ransomware, on your device. This is all done behind the scenes, so it is undetectable to the average user. Once the malware has been installed, it could harvest your sensitive information, send out more phishing messages to contacts in your address book or provide a cyber-criminal with remote access to your device.
Unfortunately, phishing messages are becoming harder and harder to identify. Since these scams are increasingly sophisticated, there is a high probability either you or someone who uses your devices will fall victim to phishing at some point. For tips on how to protect yourself from these messages, read How to Spot a Phishing Email.
What to Do If You Click on a Phishing Link
If you happen to make the mistake of clicking on a phishing link or downloading a malicious attachment, follow these steps to minimize the repercussions.
Disconnect Your Device
The first thing you need to do is immediately disconnect the compromised device from the Internet. If you are using a wired connection, the easiest way to do this is to unplug the Internet cable (ethernet cord) from your computer.
If you are connected through Wi-Fi, locate the Wi-Fi settings on your device and disconnect from the current network. If you cannot locate your Wi-Fi network settings on your device, then go directly to your Wi-Fi router and shut it off.
This will reduce the risk of malware spreading to other devices on your network, prevent the malware from sending out sensitive information from your device and keep someone from remotely accessing your device.Back Up Your Files
Now that you are disconnected from the Internet, you should back up your files. Data can be destroyed or erased in the process of recovering from a phishing attack. If you regularly back up your files using methods like an external hard drive, a USB thumb drive or cloud storage, then you may only need to back up files that have been updated or created since the last backup. Focus on protecting particularly sensitive documents and information as well as irreplaceable files like family photos and videos.
If you have never copied your files to a backup device or program, I suggest selecting one of the storage methods mentioned above. The cost of external hard drives and thumb drives has fallen considerably over the years, and they can store a significant amount of data.Scan Your System for Malware
Whom you choose to carry out this step depends on your level of technological expertise. If you are not very tech savvy, I suggest you take your device to a professional to have it checked for malware. Be sure to ask your friends and family for references. Just because someone says they fix computers or other electronic devices does not mean they know how to identify and safely remove malware.
If you want to tackle this step yourself, perform a thorough, two-step scan of your system. After you have disconnected your device from the Internet, run a complete scan with your anti-virus program. (Proceed to the next paragraph if you do not have an anti-virus program on your device.) An error message may appear, notifying you that the program could not connect to the Internet. Ignore the message. You can still run the scan without access to the Internet, and you want to avoid reconnecting, which would allow any malware to continue running its course. The scan may take some time to run, so be patient. Do not do anything else on your device during this process. You will be notified when the scan has been completed. Simply follow the program’s instructions to remove or quarantine any suspicious files that are found.
I recommend running a second scan with a free program called Malwarebytes. Use another device, not the compromised one, to connect to the Internet and download the Malwarebytes program here: https://www.malwarebytes.com/for-home/products. (I have provided the direct link because scammers often create fake websites offering “free downloads” of anti-malware software that are really just more malware in disguise.)
Download the program to a portable storage device like a thumb drive, and then use it to install the Malwarebytes program on your compromised device. During the installation period, the program may ask you if you want to upgrade to a free trial of the “premium” version. Simply decline and install the free one. Once installed, the program will ask you to update the database. Since you are still disconnected from the Internet, you will not be able to do this. Decline and move to the next step of running a complete scan on your compromised device. The scan may take a long time to run, depending on the size of your hard drive. Be patient and do not do anything else on the device while it is running.
After this second scan has finished, the program will provide you with the results. Anything suspicious will be marked. Follow the program’s steps to either clean or quarantine these files.
Please note that some malware may be disguised as legitimate operating files, making it difficult for Malwarebytes and other anti-virus programs to detect. If you are still having issues with your device or want to be certain that your system is clean, it is best to be proactive and take your device to a professional.Change Your Credentials
Malware may be used to harvest sensitive information, including online usernames and passwords, credit card numbers, bank account numbers, and other identifying information. If you think you have been tricked into acting on a phishing message, change your online credentials immediately. This applies to all online accounts—email, online banking, social media, shopping accounts, you name it.
Do not make the mistake of using the same username and password for all your online accounts. This makes it much easier for criminals to steal your credentials, access your personal information and steal your funds.Set Up a Fraud Alert
According to the FBI’s most recent annual Internet Crime Report, the American public lost a total of over $54 million to phishing attacks in 2020. To protect yourself, contact one of the major credit bureaus and ask for a free fraud alert to be placed on your credit report. This may seem like overkill, but it is better to be safe than sorry. The three major bureaus are Experian, Equifax and TransUnion. Once you have placed a fraud alert with one of these bureaus, they are required by law to notify the other two on your behalf. This will make it more difficult for fraudsters to open new accounts in your name.
Proceed With Caution
Phishing text messages and emails have become a dangerous yet unavoidable threat in the digital age. Your best protection is to err on the side of caution and use the “delete” button on emails and texts that seem sketchy. Remember, a legitimate organization or business will never ask you to share sensitive, personal information via insecure channels like email, text or pop-up messages. If the message is truly important, the sender will attempt to contact you through verified methods like telephone or snail mail.